Research Project
Privacy Risks in Data Collection and Storage
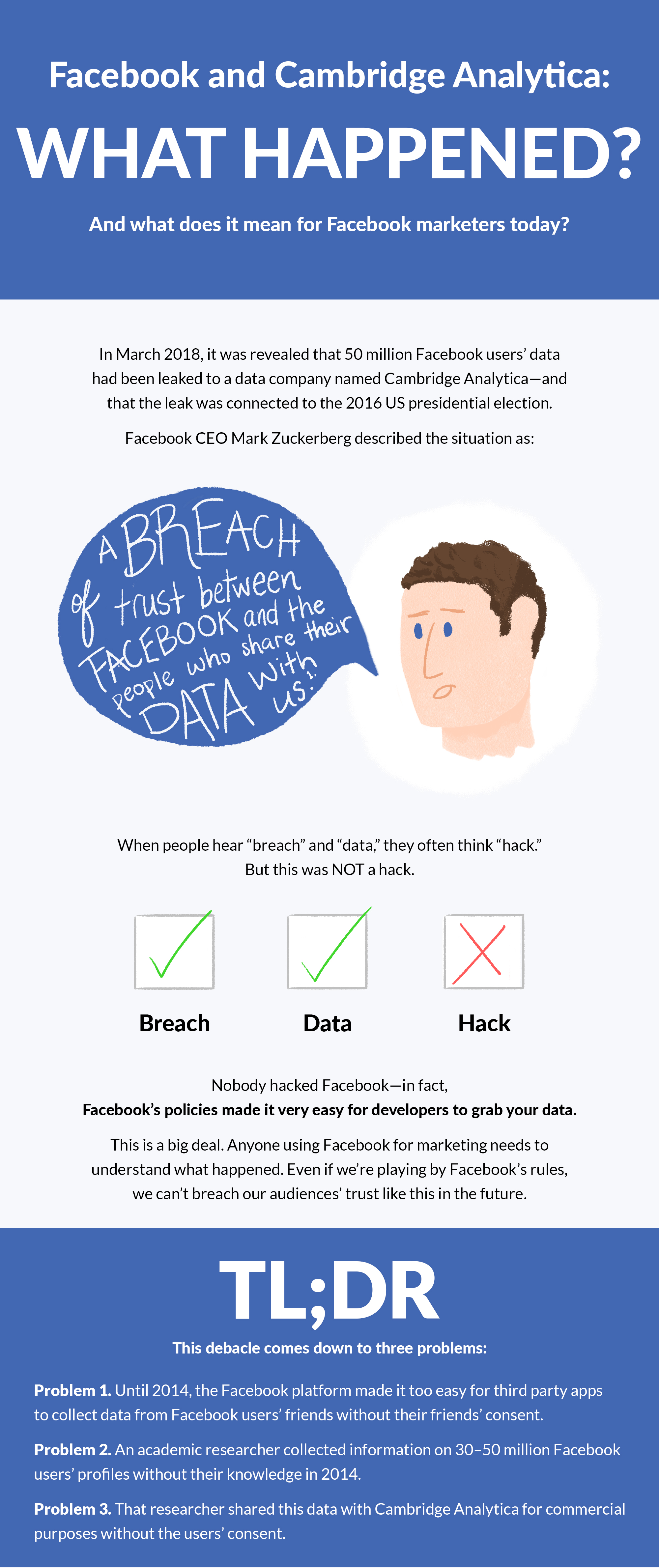
Modern digital services rely heavily on collecting and storing personal data—such as names, contact details, browsing activity, locations, and purchasing habits—to improve products and personalize user experiences, but this creates major privacy risks because centralized databases are attractive targets for hackers and can be exposed through weak security practices. Beyond breaches, companies may also misuse data by sharing or selling it without clear user consent, prompting regulations like GDPR and CCPA to give people more control. High‑profile incidents such as Facebook’s 2018 Cambridge Analytica scandal highlight how poorly governed data access and sharing can lead to large‑scale misuse of personal information.
Sources
Cybersecurity & Infrastructure Security Agency
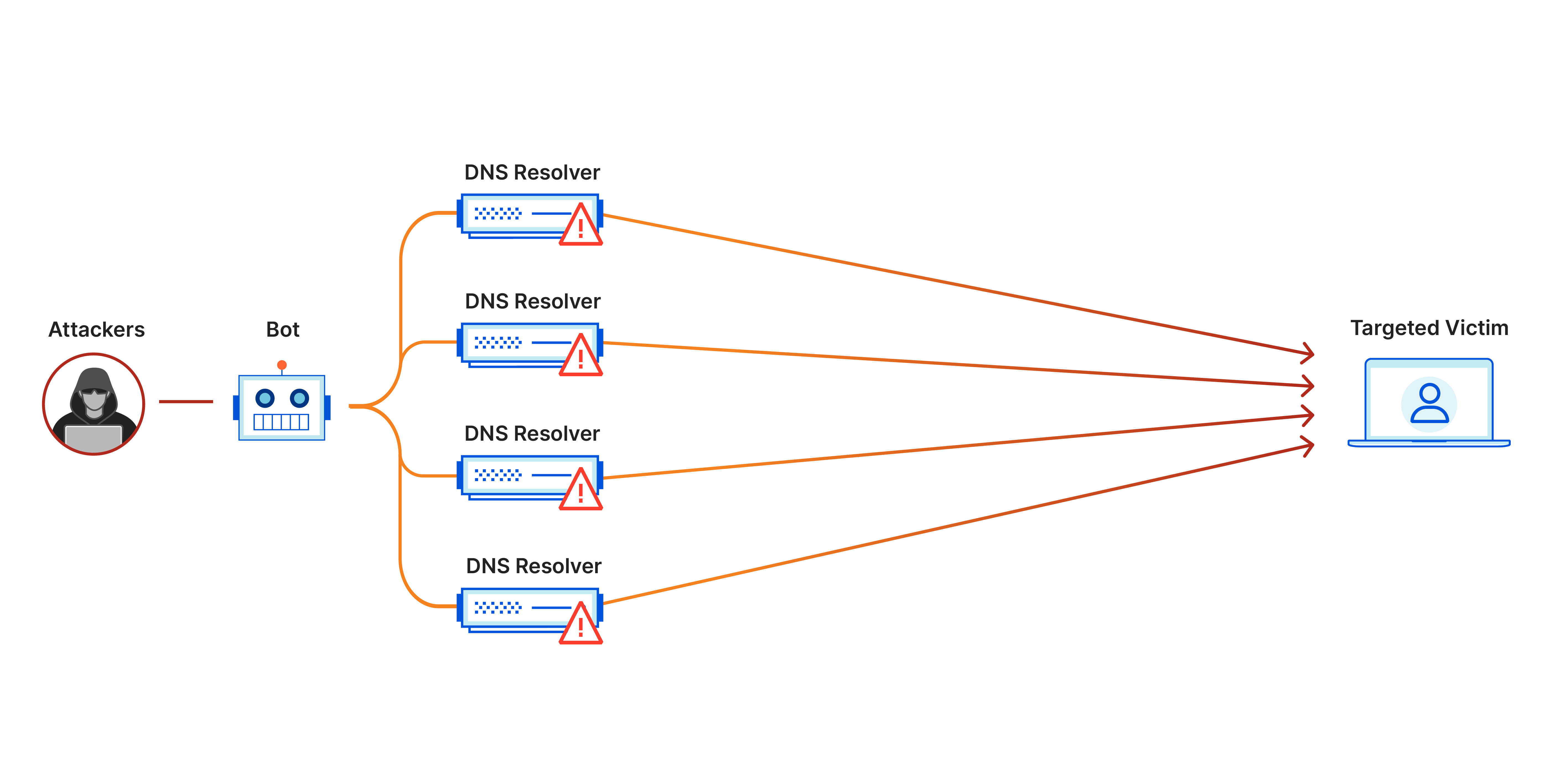
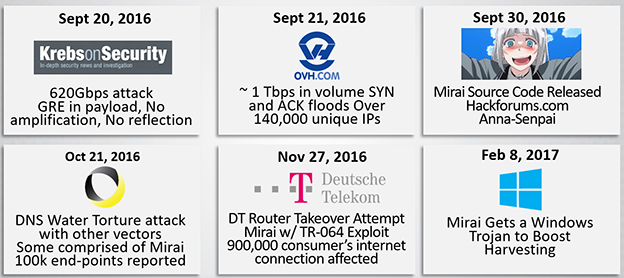
Misuse and Protection of Computing Resources
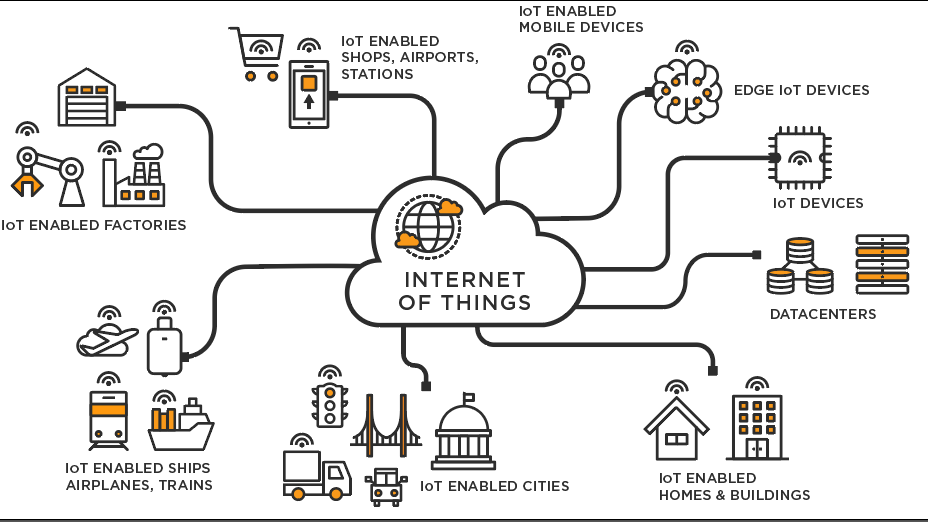
Cybercriminals often exploit computing resources—servers, networks, and personal devices—to carry out illegal activities like DDoS attacks, spam campaigns, or unauthorized cryptocurrency mining, draining processing power and disrupting normal operations. A major method involves creating botnets, where malware-infected devices are remotely controlled to launch large‑scale attacks that can crash systems or cause widespread outages. To defend against this misuse, organizations rely on tools such as firewalls, antivirus software, intrusion detection systems, regular updates, and strong password practices, along with monitoring to spot suspicious activity. The risks were highlighted in the 2016 Mirai botnet incident, where thousands of vulnerable IoT devices were hijacked and used to execute a massive DDoS attack that temporarily took down major sites like Twitter, Netflix, and Reddit.
Sources
Cybersecurity & Infrastructure Security Agency
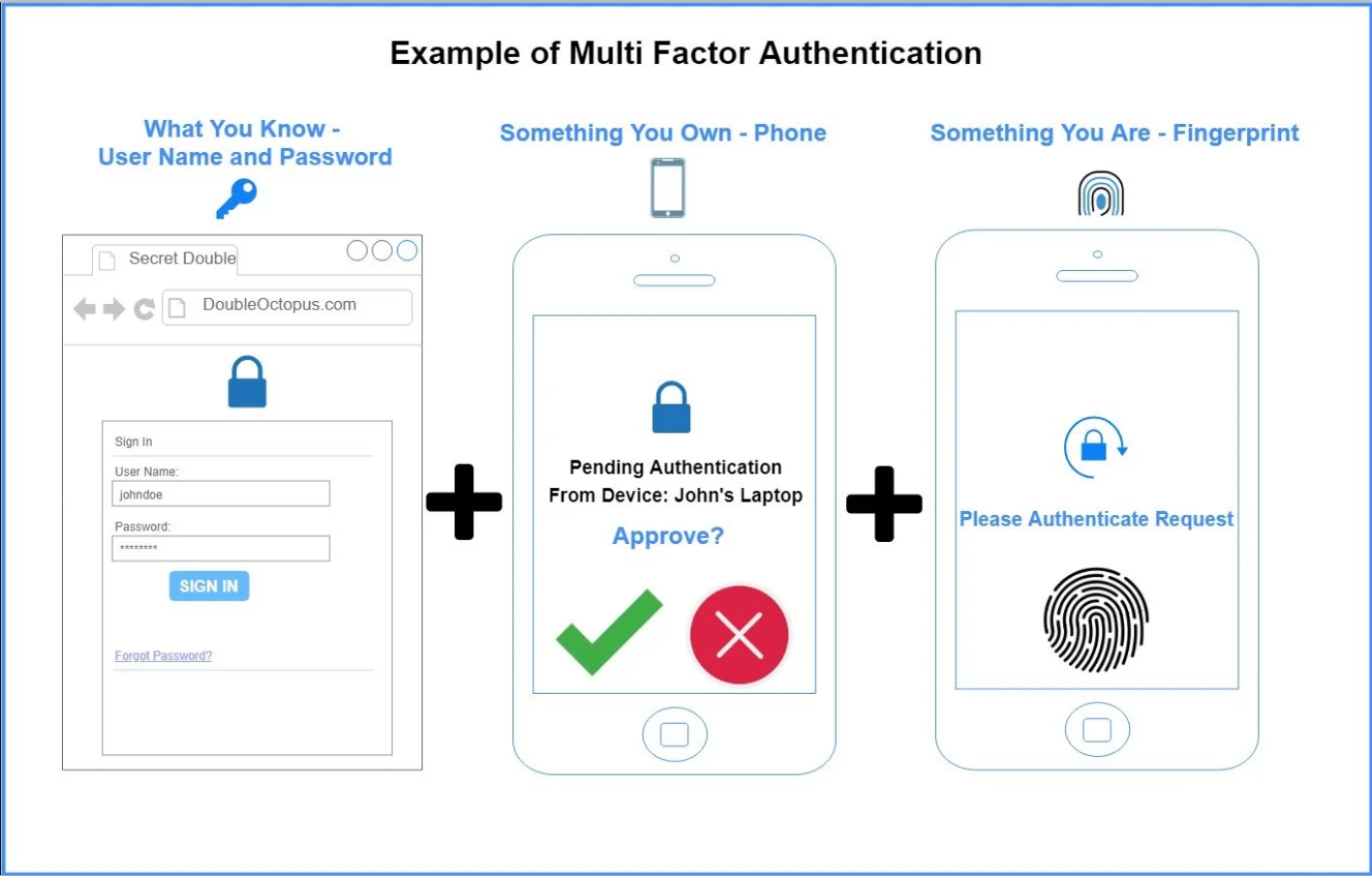
Unauthorized Access to Information
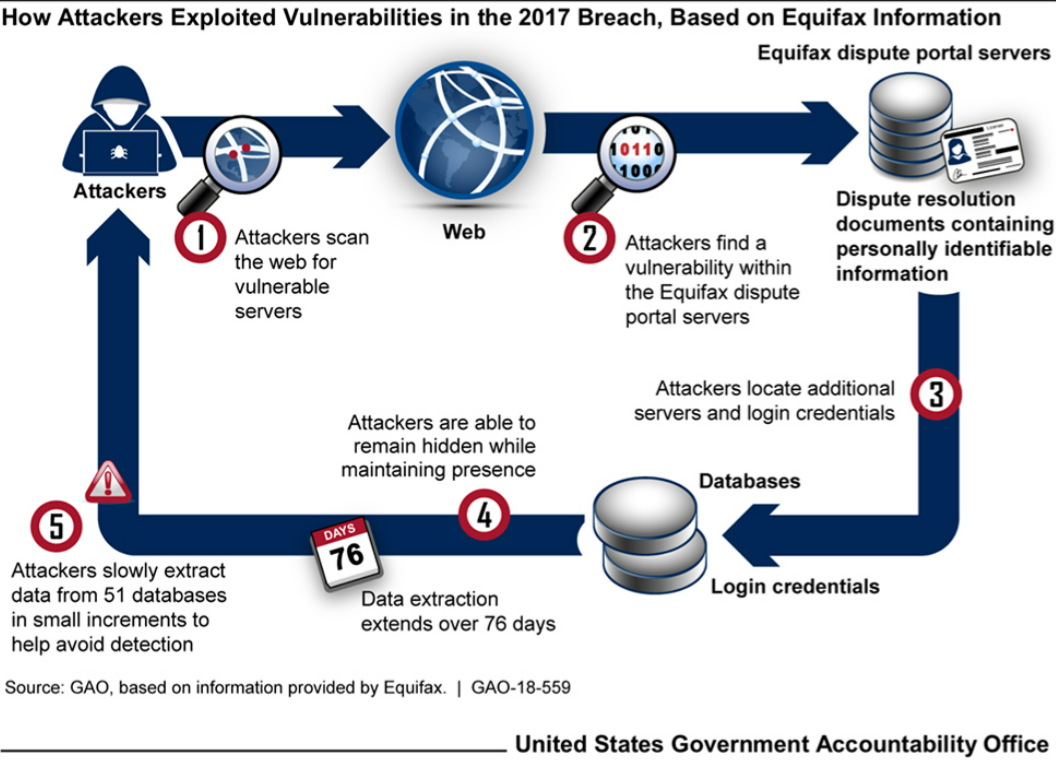
Unauthorized access happens when attackers break into systems or accounts using tactics like phishing, malware, password cracking, or exploiting software flaws, allowing them to steal financial data, personal information, or confidential business records. Phishing is especially common, tricking users into revealing login credentials through messages that appear legitimate. Organizations reduce these risks by using multi‑factor authentication, encryption, regular updates, network monitoring, and user training to spot suspicious emails. The dangers of weak security were made clear in the 2017 Equifax breach, where an unpatched vulnerability allowed attackers to access sensitive data from about 147 million people.
Sources
Cybersecurity & Infrastructure Security Agency
Benefits and Risks of Computing Innovations
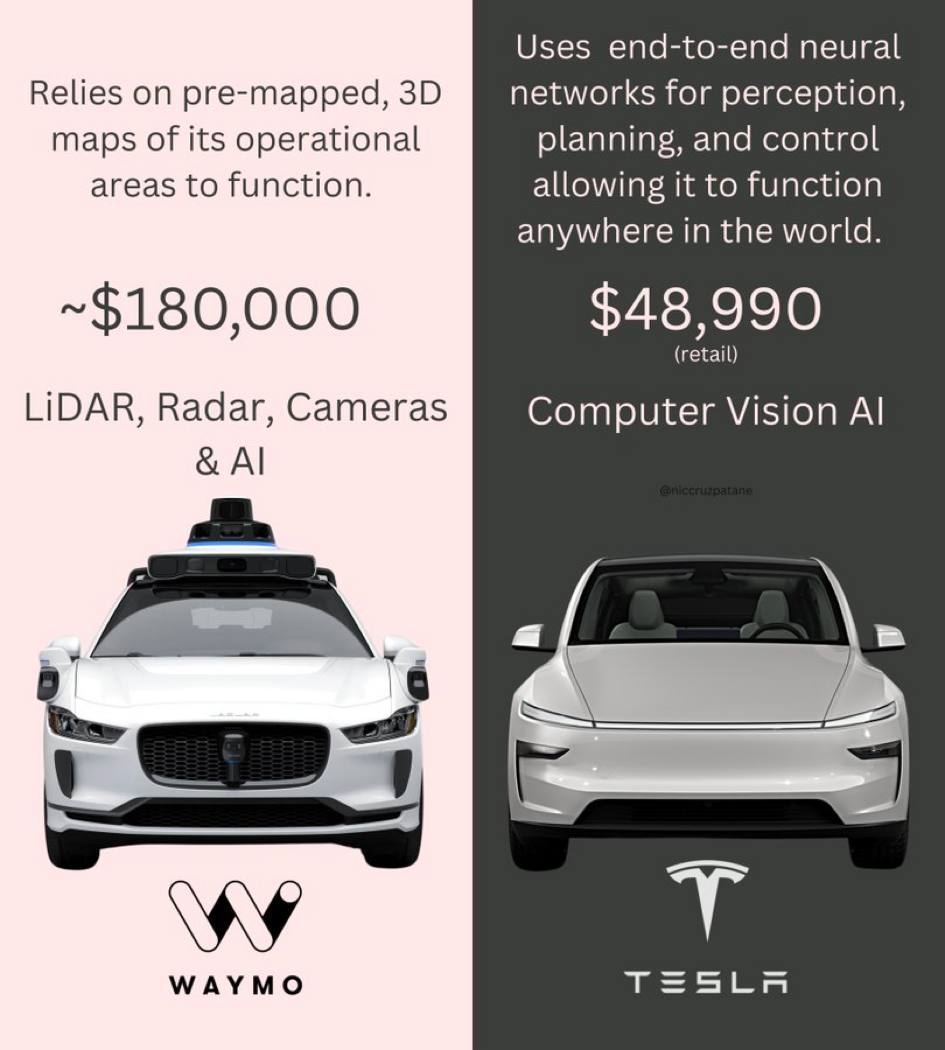
Computing innovations like artificial intelligence, cloud platforms, and the Internet of Things have greatly enhanced modern life by enabling automation, improving healthcare, expanding communication, and boosting productivity, but they also introduce risks such as algorithmic bias, privacy concerns, and security vulnerabilities in connected devices. Technologies often create unintended consequences—social media, for example, was designed for connection but has also fueled misinformation, harassment, and data misuse—highlighting the need for responsible development and regulation. Ethical issues around AI decision‑making, facial recognition, and data handling continue to grow, while real‑world cases like accidents involving self‑driving cars from companies such as Tesla and Waymo show how safety, liability, and transparency remain major challenges as these innovations evolve.
Sources
Image Sources